Arthur Besse
cultural reviewer and dabbler in stylistic premonitions
- 31 Posts
- 117 Comments
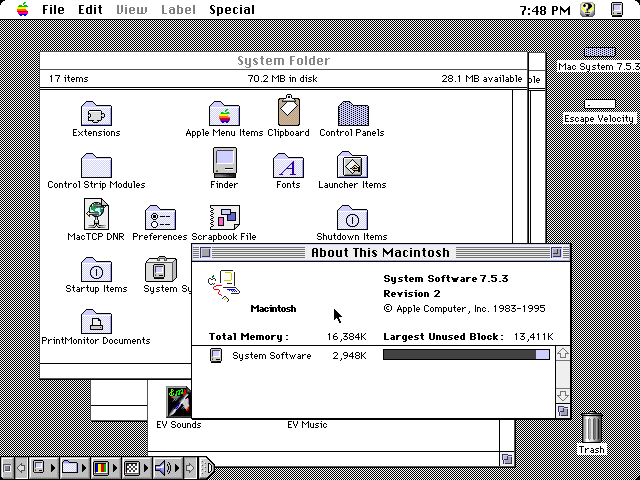
python -c 'print((61966753*385408813*916167677<<2).to_bytes(11).decode())'how?
$ python >>> b"Hello World".hex() '48656c6c6f20576f726c64' >>> 0x48656c6c6f20576f726c64 87521618088882533792115812 $ factor 87521618088882533792115812 87521618088882533792115812: 2 2 61966753 385408813 916167677

 16·27 days ago
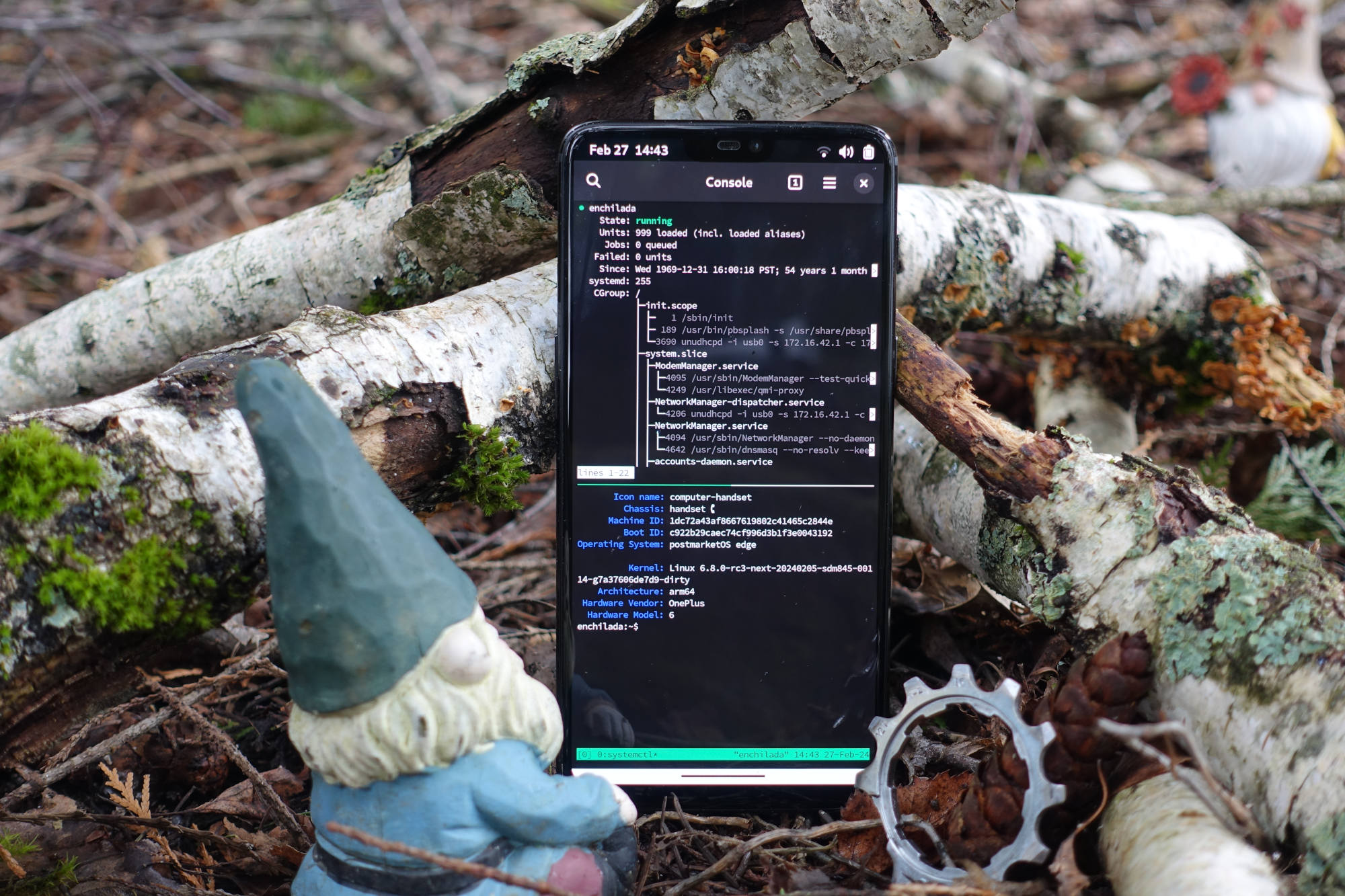
16·27 days agoYou may not like it, but this is what peak performance looks like.

 38·1 month ago
38·1 month agoI initially found git a bit confusing because I was familiar with mercurial first, where a “branch” is basically an attribute of a commit and every commit exists on exactly one branch. It got easier when I eventually realized that git branches are just homeomorphic endofunctors mapping submanifolds of a Hilbert space.

 2·1 month ago
2·1 month agoE: old thinkpad gang input: take the time to reapply thermal grease to the cpu at some point. It makes a huge difference.
What’s a “gang input”?
😂 it’s an input to this discussion from a member of the group of people (“gang”) who have experience with old thinkpads. and yes, if your old thinkpad (or other laptop) is overheating and crashing, reapplying the thermal paste is a good next step after cleaning the fans.

 5·2 months ago
5·2 months agoxzbot from Anthony Weems enables to patch the corrupted liblzma to change the private key used to compare it to the signed ssh certificate, so adding this to your instructions might enable me to demonstrate sshing into the VM :)
Fun :)
Btw, instead of installing individual vulnerable debs as those kali instructions I linked to earlier suggest, you could also point debootstrap at the snapshot service so that you get a complete system with everything as it would’ve been in late March and then run that in a VM… or in a container. You can find various instructions for creating containers and VMs using debootstrap (eg, this one which tells you how to run a container with
systemd-nspawn; but you could also do it with podman or docker or lxc). When the instructions tell you to rundebootstrap, you just want to specify a snapshot URL likehttps://snapshot.debian.org/archive/debian/20240325T212344Z/in place of the usual Debian repository url (typicallyhttps://deb.debian.org/debian/).

 27·2 months ago
27·2 months agoA daily ISO of Debian
testingor Ubuntu 24.04 (noble) beta from prior to the first week of April would be easiest, but those aren’t archived anywhere that I know of. It didn’t make it in to any stable releases of any Debian-based distros.But even when you have a vulnerable system running sshd in a vulnerable configuration, you can’t fully demo the backdoor because it requires the attacker to authenticate with their private key (which has not been revealed).
But, if you just want to run it and observe the sshd slowness that caused the backdoor to be discovered, here are instructions for installing the vulnerable liblzma deb from snapshot.debian.org.

 2·2 months ago
2·2 months agobecause i thought the situation described by the post was tragicomic (as was somewhat expressed by the line from it quoted in the post title)

 1·2 months ago
1·2 months agoYou can use Wireshark to see the packets and their IP addresses.
https://www.wireshark.org/download.html
https://www.wireshark.org/docs/
A word of warning though: finding out about all the network traffic that modern software sends can be deleterious to mental health 😬

 2·2 months ago
2·2 months agoI do have wireguard on my server as well, I guess it’s similar to what tailscale does?
Tailscale uses wireguard but adds a coordination server to manage peers and facilitate NAT traversal (directly when possible, and via a intermediary server when it isn’t).
If your NAT gateway isn’t rewriting source port numbers it is sometimes possible to make wireguard punch through NAT on its own if both peers configure endpoints for eachother and turn on keepalives.
Do you know if Yggdrasil does something similar and if we exchange data directly when playing over Yggdrasil virtual IPv6 network?
From this FAQ it sounds like yggdrasil does not attempt to do any kind of NAT traversal so two hosts can only be peers if at least one of them has an open port. I don’t know much about yggdrasil but from this FAQ answer it sounds like it runs over TCP (so using TCP applications means two layers of TCP) which is not going to be conducive to a good gaming experience.
Samy Kamkar’s amazing pwnat tool might be of interest to you.

 2·2 months ago
2·2 months agoI have a device without public IP, AFAIK behind NAT, and a server. If I use bore to open a port through my server and host a game, and my friends connect to me via IP, will we have big ping (as in, do packets travel to the server first, then to me) or low ping (as in, do packets travel straight to me)?
No, you will have “big ping”. bore (and everything on that page i linked) is strictly for tunneling which means all packets are going through the tunnel server.
Instead of tunneling, you can try various forms of hole punching for NAT traversal which, depending on the NAT implementation, will work sometimes to have a direct connection between users. You can use something like tailscale (and if you want to run your own server, headscale) which will try its best to punch a hole for a p2p connection and will only fall back to relaying through a server if absolutely necessary.

 5·2 months ago
5·2 months agoSee https://github.com/anderspitman/awesome-tunneling for a list of many similar things. A few of them automatically setup letsencrypt certs for unique subdomains so you can have end-to-end HTTPS.

 203·2 months ago
203·2 months agoyou don’t see any downside to nuclear escalation?

 7·2 months ago
7·2 months agoWho is we???
Perhaps OP is a member of the US congress, trying to figure out what to vote for? 🤪
There is a nice sample of Michael Parenti talking about this kind of use of the word “we” at the beginning of this song. (lyrics here)

 53·3 months ago
53·3 months agothe US didn’t have to coerce them to kick him out.
You think the $4.2B IMF loan package they got 30 days before his expulsion wasn’t contingent on revoking his asylum? Here is evidence that it was, two months before it happened.
He essentially got kicked out for installing spyware and listening devices into the embassy’s private network.
What? The listening devices and hidden cameras were in fact installed by the Spanish private security company who was ostensibly working for the embassy but who it turned out was also working for the CIA, for the purpose of spying on Assange (including in the bathroom, where he would go to meet with his lawyers due to his suspicion that the other rooms had been bugged), as has been well documented in both US and Spanish courts:

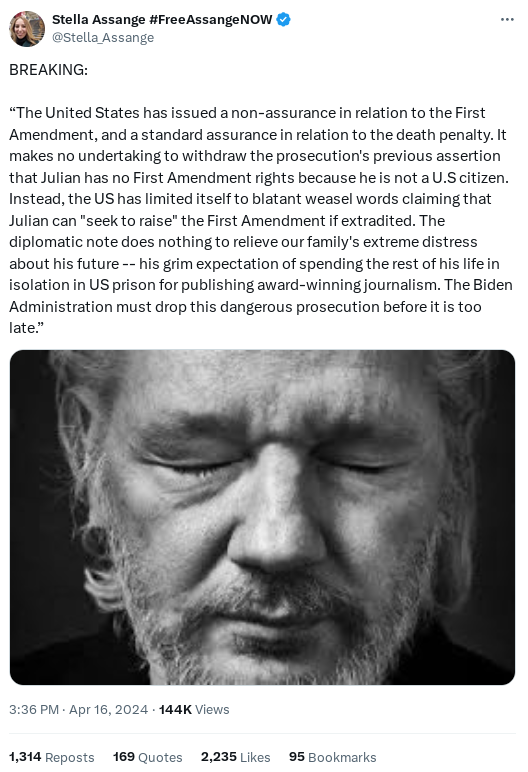
 141·3 months ago
141·3 months agoWhat is it that people in the UK don’t understand about ‘indeterminate detention without charge’?
He was detained without charge for many years, but there are charges now: the US unsealed their 2018 indictment against him immediately after they coerced Ecuador into revoking his asylum in April 2019, and they added more charges a month later.
As the linked article explains, he is currently charged with 17 counts of espionage and 1 count of conspiracy to commit computer intrusion. He remains in His Majesty’s Prison Belmarsh while fighting the US’s extradition request.
See also https://en.wikipedia.org/wiki/Indictment_and_arrest_of_Julian_Assange

 5·3 months ago
5·3 months agoTuta is most likely a honeypot, and in any case it is pseudo-open source so it’s offtopic in this community.
As the image transcript in the post body explains, the image at the bottom is a scene from a well-known 1998 film (which, according to Wikipedia, was in 2014 selected for preservation in the United States National Film Registry by the Library of Congress as being “culturally, historically, or aesthetically significant”).
This meme will not make as much sense to people who have not seen the film. You can watch the referenced scene here. The context is that the main character, The Dude (played by Jeff Bridges) has recently had his private residence invaded by a group of nihilists with a pet marmot (actually portrayed by a ferret) and they have threatened to “cut off his Johnson”. In an attempt to express sympathy, The Dude’s friend Walter (played by John Goodman) points out that, in addition to the home invasion and threats, the nihilists’ exotic pet is also illegal. The Dude’s retort “what, are you a fucking park ranger now” is expressing irritation with that observation, because it is insignificant compared with the threat of the removal of his penis.
This meme attempts to draw a parallel between this humorous scene and XZ developer Lasse Collin’s observation that the XZ backdoor was also a violation of Debian’s software licensing policies.
Thank you for reading my artist’s statement.

 3·3 months ago
3·3 months agoOk, you and @[email protected] are both mods of /c/[email protected] now. Thanks!

















lol, i just accepted the title tag from the page which the create post form auto-filled 🤡