

I can excuse attempting to compromise millions of computer systems worldwide for nefarious purposes but I draw the line at violating the contributor guidelines of an opensource project.


I can excuse attempting to compromise millions of computer systems worldwide for nefarious purposes but I draw the line at violating the contributor guidelines of an opensource project.


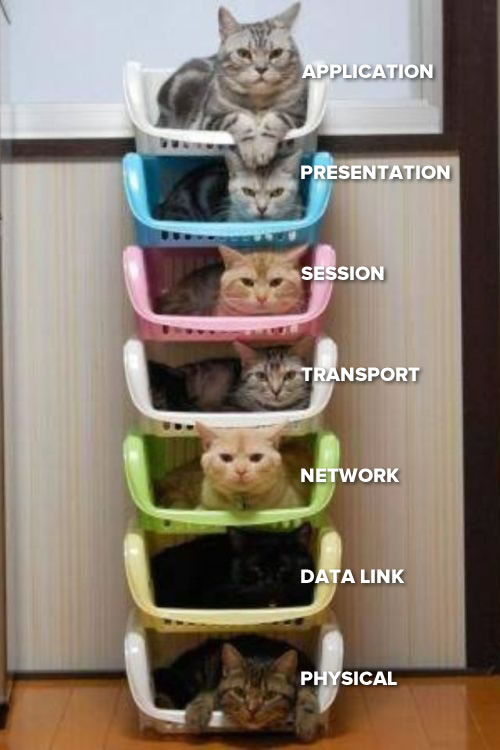
The top cat uses ports to sort messages based on application.

Think pigeon holes, applications usually use protocols which are assigned a number by convention. The application gets it’s message out of it’s assigned ports instead of having to sort through all the messages.


he’s fired


here I am feeling guilty sometimes making a comment halfway through a 200 comment thread before scrolling on to find someone else already made the same joke while this mf making smug comments when they’ve not even read half the headline.


Linus Torvalds. He’s making a list.


Here is a really interesting video on lightbulbs which goes into how the light bulb cartel standard was more of a min-maxing of lifespan vs energy cost vs brightness than it was planned obsolescence.
I unfortunately can’t speak to this directly as I don’t have direct knowledge of ad blockers.
Yeah me too 


You could use Insular to quarantine your untrusted apps into their own profile (different permissions, file directory etc) and then transfer the individual photos to the “work” profile to access them with whatsapp.


I did the same thing starting probably around the same time as you except that did it start working for me 5 years ago and I haven’t gone back to windows.


So they basically said “doesn’t count if there is jobs growth”. As long as you can keep creating 10 precarious gig worker jobs for every 9 full time jobs that are eliminated then the economy is doing great!


There are two doors, one is labelled “Leopards that will eat your face” the other “Cat cafe” both lead into the same leopard cage.


how did the power user payola compare to xi bucks?
“if” gcc had a Ken Thompson hack how do you secure checks notes anything